Fortinet Firewall (virtual) appliances are widely deployed within corporate and large-scale environments. You can position Fortinet Firewalls in your cloud tenants or on the edge and core of your network. Fortinet Firewalls work decently to dictate network segmentation and semi-regulate traffic based on known network protocols and VLANs.
Fortinet offers Web Filtering and Threat Intelligence capabilities on a subscription basis called FortiGuard. FortiGuard can flag possible unwanted and malicious network traffic. Although FortiGuard can be of used to detect malicious network activity, ForitGuard does not always flag all possible malicious network traffic, nor does it always block known and unknown network security threats. This is why we forward Forti logging to Sentinel SIEM (Security Information and Event Management) to complement the FortiGuard service.
Fortigate Firewall Threat Hunting
Sentinel is Microsoft's cloud-native SIEM solution that can be used to analyze Fortinet, Palo Alto, CheckPoint, and Cisco firewall network traffic. In Sentinel, you can check if Indicators of Attack (IoA) such as an IP address, a device based on MAC address, or specific network traffic is seen across other services, applications, and applications within your network. Furthermore, you can rely on other integrated third-party Threat Intelligence sources and IoA's. Moreover, we can now leverage Sentinel for correlations, alerting, and even automated isolation or blocking actions (SOAR).
Natively, Sentinel provides a Fortinet data connector, which means it can automatically map most Fortigate data log fields to Sentinel Log Analytics fields. Sentinel also provides an abstract non-actionable security Workbook dashboard, which we found rather useless.
First, your firewall should forward the log traffic in Syslog Common Event Format (CEF) format to a self-hosted Linux-based VM (Virtual Machine), which in turn forwards the Firewall Syslog CEF logging with Python cef_installer.py to your cloud-native Sentinel Workspace. This process is shown in Figure 1:
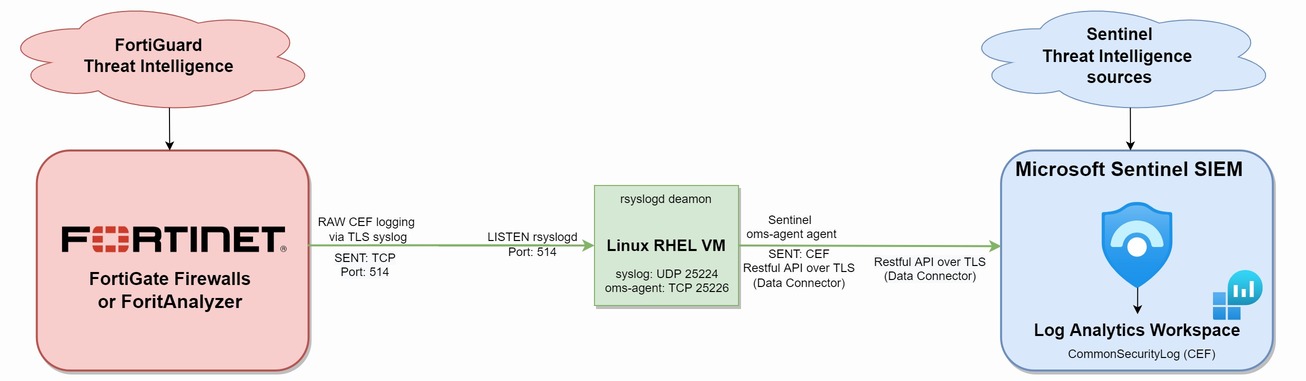
Figure 1: Fortinet connecting to Sentinel Workspace
Please note that forwarding network logging can be costly, depending on your baseline network traffic (approximately 2x$2.46 dollar per GB as of this date). We advise you to first conduct a Sentinel costs analysis or use the costs preview feature in Sentinel.
This blog post shares 5 Fortinet Firewall SOC threat hunting use-cases to monitor and alert on possible suspicious network activity, which could be an IoA. Most of the below use-cases are crafted by thinking like a malicious actor. We also consider the MITRE ATT&CK framework into account to mirror the different Sentinel use-cases against known attack phases. You can use the FortiGate document library to craft your own KQL (Kusto Query Language) use-cases
1. Malicious IP address detected based on Sentinel Threat Intelligence indicators. Note: configure your Sentinel Threat Intelligence sources first.
//cryptsus.com - we craft cyber security solutions
//Malicious IP address detected based on Sentinel Threat Intelligence indicators
CommonSecurityLog
| where DeviceVendor == "Fortinet"
| where DeviceAction != "deny"
| distinct DestinationIP
| project DestinationIP
//compare if any destination IP matches the Threat Intelligence IP database
| join kind = inner (
ThreatIntelligenceIndicator
| where NetworkIP != ''
) on $left.DestinationIP == $right.NetworkIP
| project-rename Source_IP = DestinationIP
| project-rename Malicious_IP = NetworkIP
| project TimeGenerated, Source_IP, ConfidenceScore, ThreatType, Malicious_IP, AdditionalInformation2. Malicious DNS name detected based on Sentinel Threat Intelligence indicators:
//cryptsus.com - we craft cyber security solutions
//Malicious DNS name detected based on Sentinel Threat Intelligence indicators
CommonSecurityLog
| where DeviceVendor == "Fortinet"
| where DeviceAction != "deny"
| distinct DestinationHostName
| project DestinationHostName
//compare if any destination domain name matches the Threat Intelligence database
| join kind = inner (
ThreatIntelligenceIndicator
| where DomainName != ''
) on $left.DestinationHostName == $right.DomainName3. Malicious network traffic detected from LAN to WAN:
//cryptsus.com - we craft cyber security solutions
//Malicious network traffic detected from LAN to WAN
CommonSecurityLog
| where DeviceVendor == "Fortinet"
| where isnotempty(IndicatorThreatType)
| where isempty(DestinationHostName)
| where DeviceOutboundInterface isnotempty(DeviceOutboundInterface)
| where DeviceAction != "deny" and DeviceAction != "close" and DeviceAction != "blocked"
| mv-expand todynamic(IndicatorThreatType)
| where ReportReferenceLink has "?tags="
| extend ReportReferenceLink=split(ReportReferenceLink,"=",1)
| mv-expand ReportReferenceLink to typeof(string)
| extend MalwareType=split(ReportReferenceLink, "&")
| mv-expand MalwareType to typeof(string)
| where MalwareType <> "languageCode"
| extend identified_application = split(AdditionalExtensions, ";")
| project TimeGenerated, IndicatorThreatType, ApplicationProtocol, SourceIP, SourcePort, Message, identified_application[23], identified_application[21], DeviceOutboundInterface, ThreatConfidence, MalwareType, MaliciousIPCountry, DestinationIP, DestinationPort, DeviceAction, Activity
| order by TimeGenerated4. Tor network traffic detected from LAN to WAN:
//cryptsus.com - we craft cyber security solutions
//Tor network traffic detected from LAN to WAN
let tor_exit_nodes = materialize (
(externaldata(exit_node: string ) [@"https://raw.githubusercontent.com/SecOps-Institute/Tor-IP-Addresses/master/tor-exit-nodes.lst"]
with (format="txt"))
| project exit_node
| summarize by exit_node);
search in (CommonSecurityLog)
| where DeviceVendor == "Fortinet"
TimeGenerated > ago(30d)
| extend additional_fields = split(AdditionalExtensions, ";")
| where SourceIP in(tor_exit_nodes)
| where SimplifiedDeviceAction != "close"
| where SimplifiedDeviceAction != "Deny"
| project $table, TimeGenerated, DeviceOutboundInterface, SourceIP, SourcePort, DestinationIP, DestinationPort, Activity, DeviceAction
| sort by TimeGenerated5. Unwanted or malicious applications detected:
//cryptsus.com - we craft cyber security solutions
//Unwanted or malicious applications detected
CommonSecurityLog
| where DeviceVendor == "Fortinet"
| where DeviceAction == "accept"
| extend additional_fields = split(AdditionalExtensions, ";")
| where additional_fields[22] == "ad.apprisk=high" or additional_fields[22] == "ad.apprisk=critical"
| summarize sessions=count() by category = tostring(additional_fields[21]), application = (tostring(additional_fields[20]))
| sort by sessions




